How to use URLSCAN part4
This is the part 4 and the last of (How to use URLSCAN part3 – osintafrica)
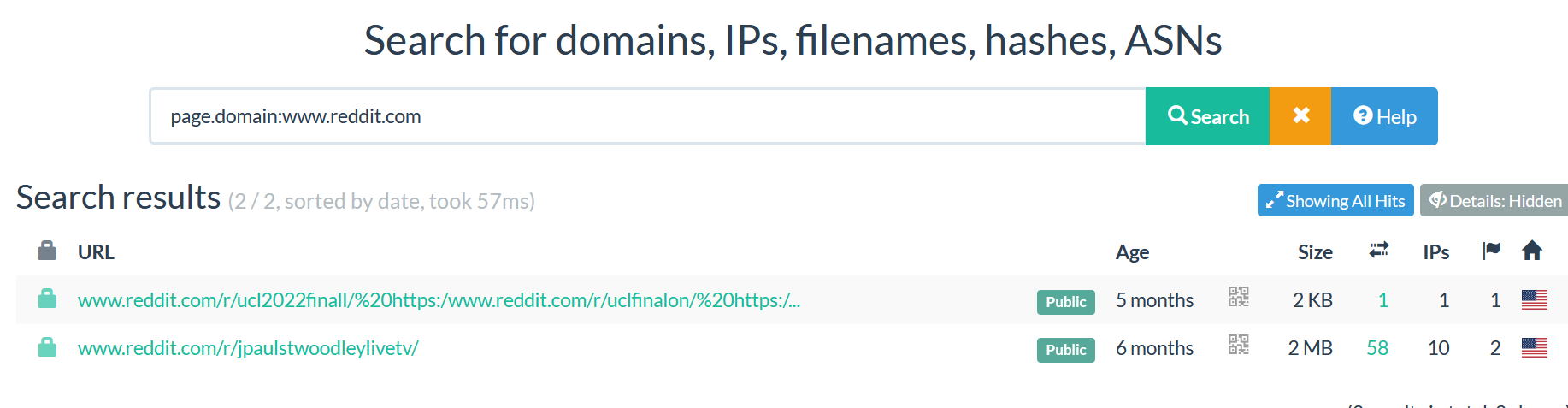
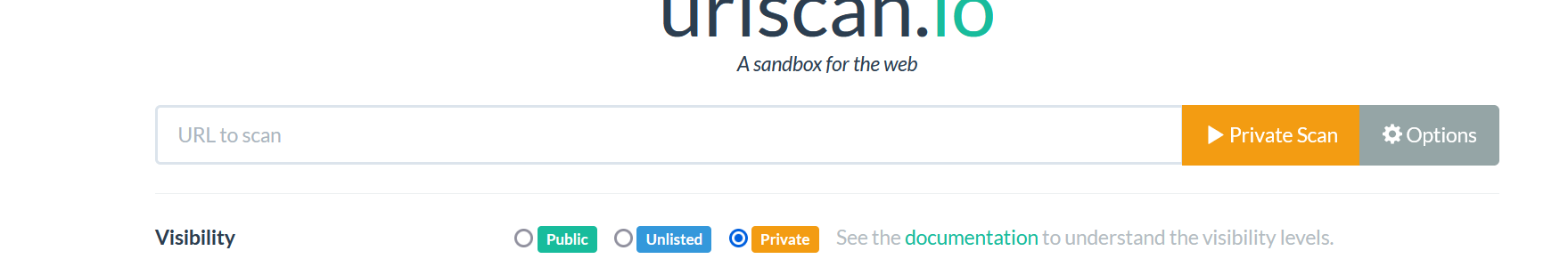
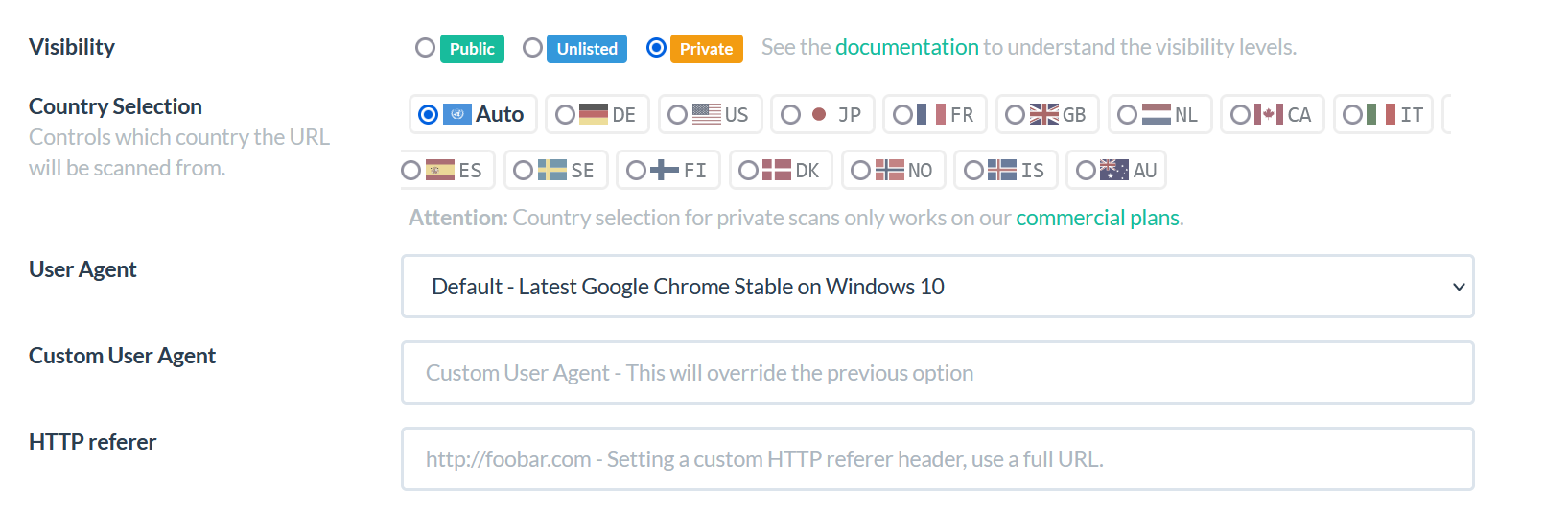
- SEARCH
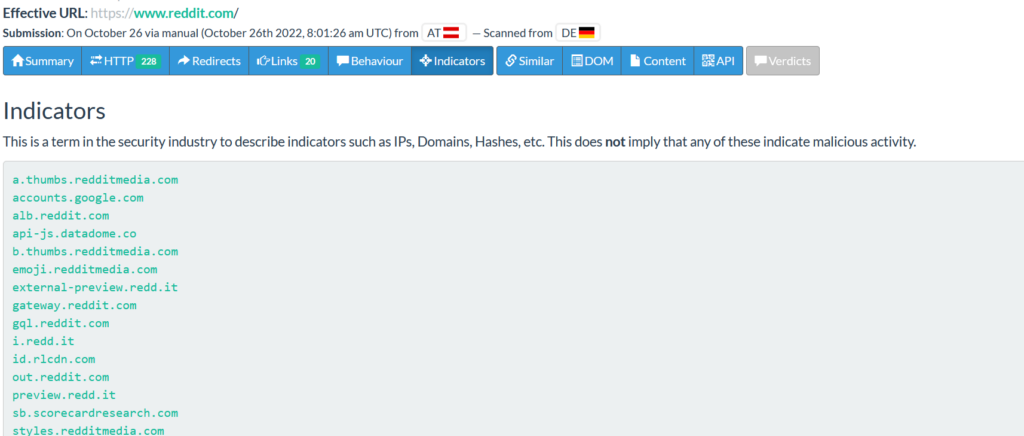
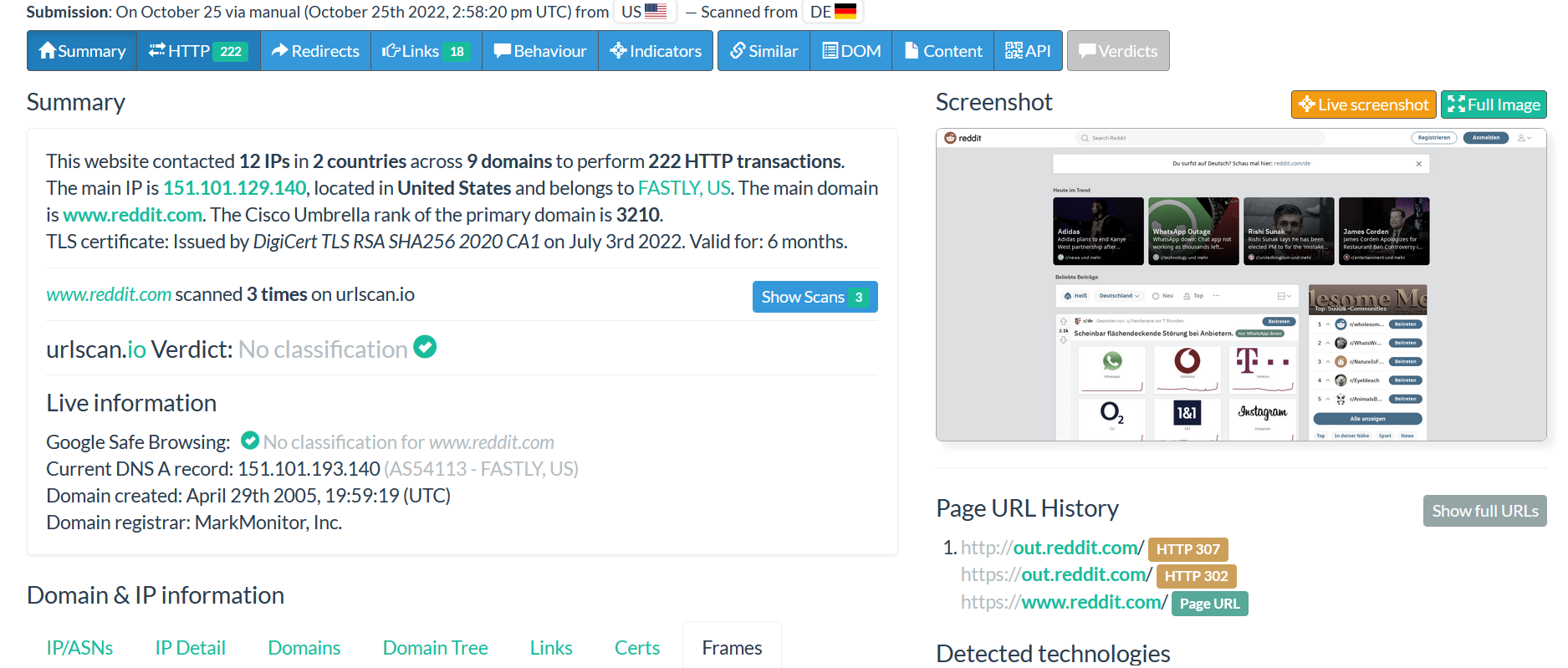
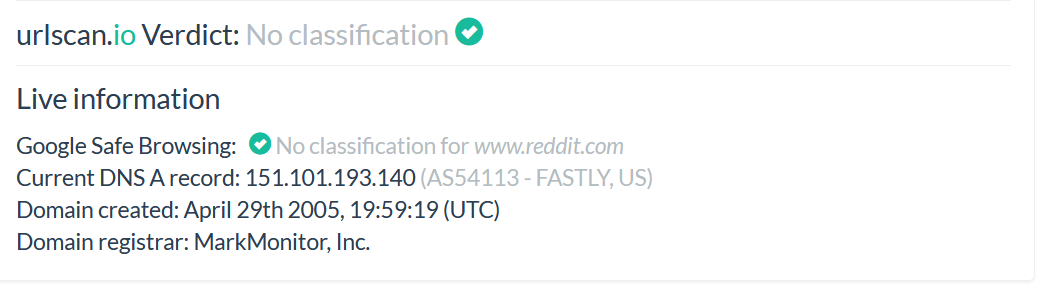
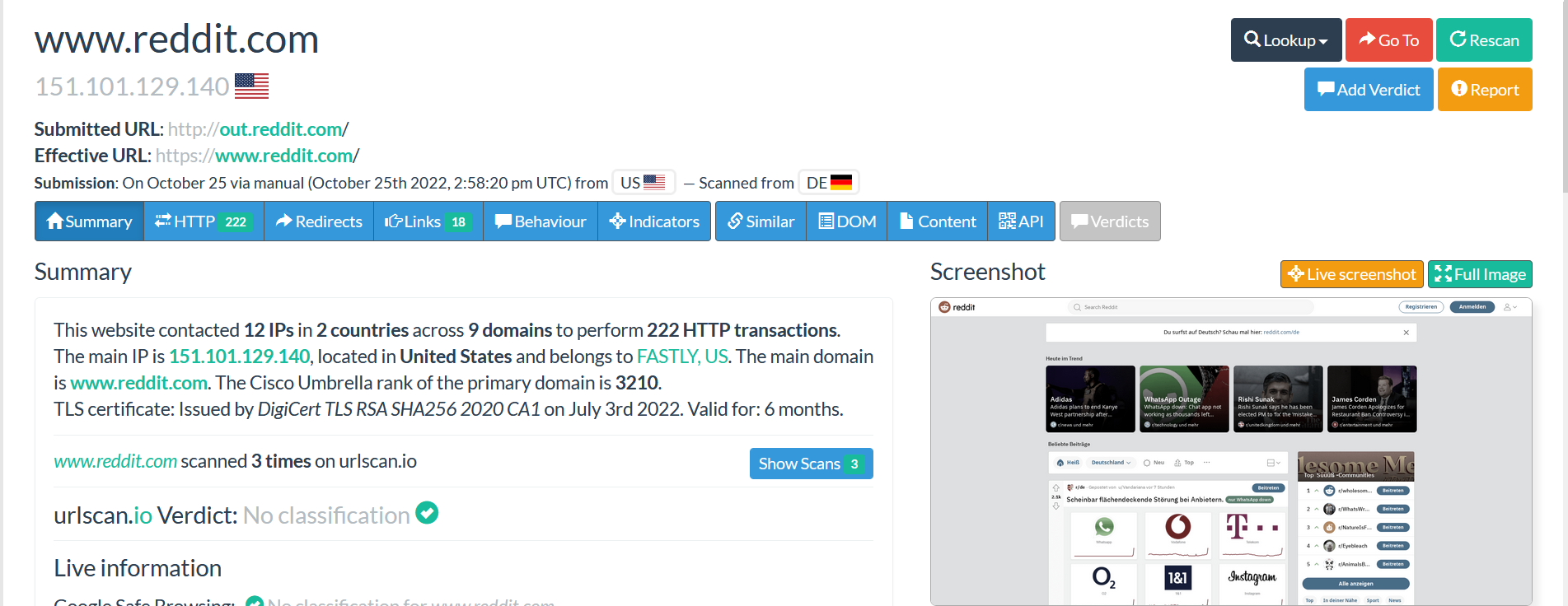
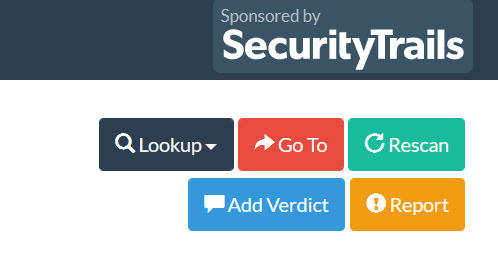
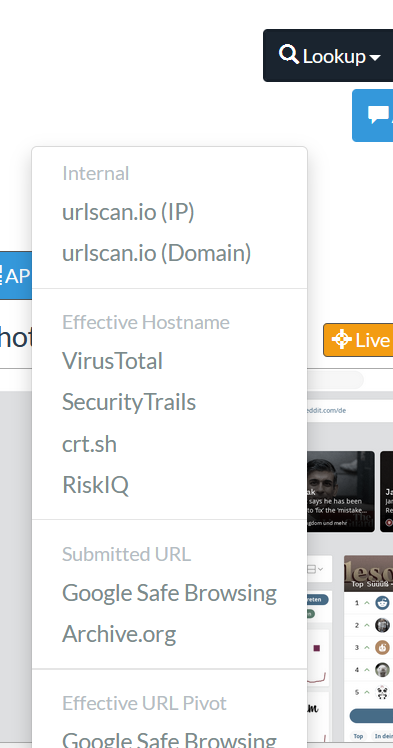
URLSCAN can help to perform different types of searches to find more information about an indicator such as IP address, domain, file, hash, ASN number and others.
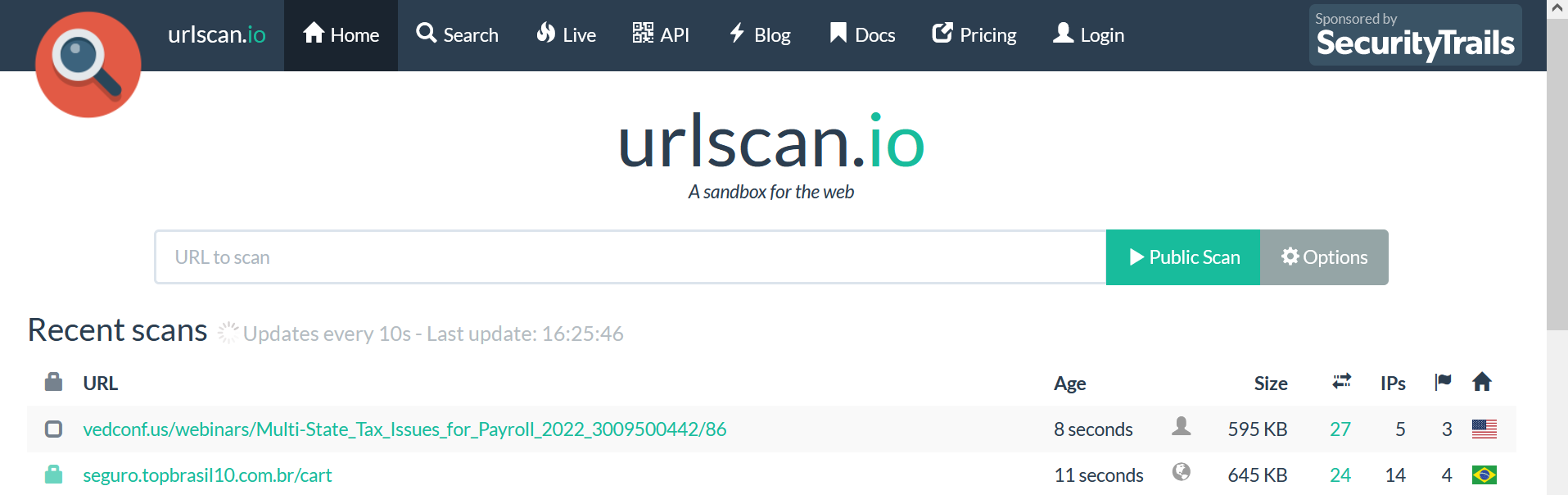
Click on the “Search” button.
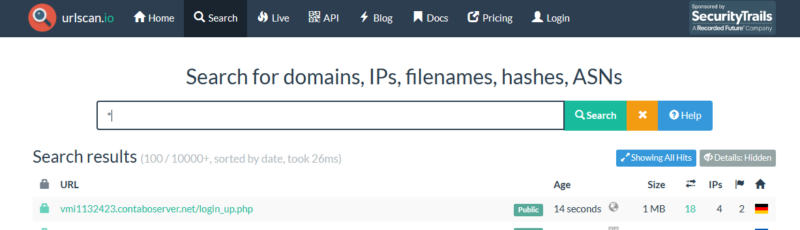
It is very important to first read the documentation. Click on the “Help” button to read about how to perform different searches.
Let’s give some examples of queries that we can perform in the Search menu.
- Search for domain
If you want to find more information about a specific domain such as how the domain looked before and the connection between the domain with others domains or website, you can use the “domain:” query. We will give an example using microsoft.com.
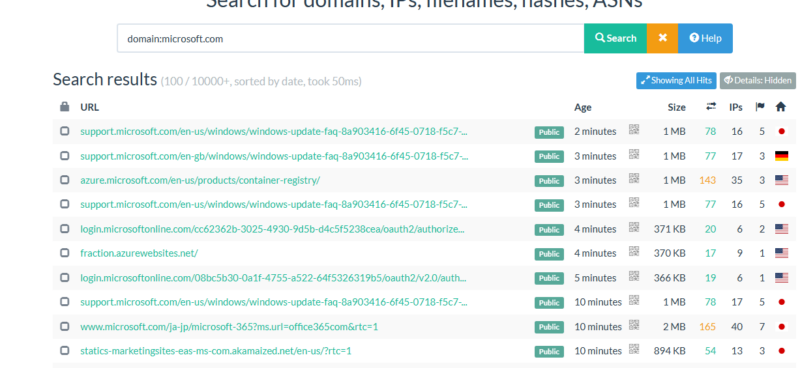
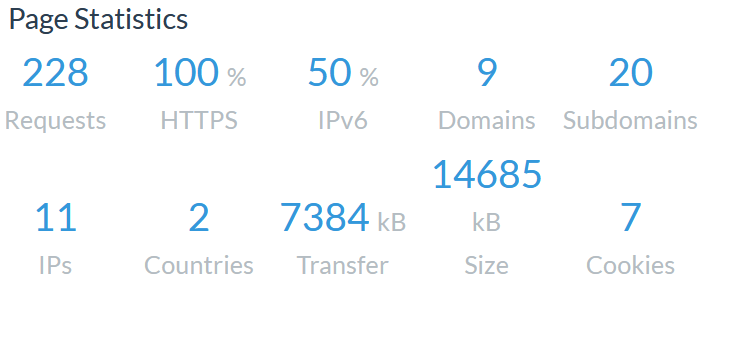
In the image above, we can see the search result showing the domain Microsoft.com with different subdomains related to Microsoft.com and others domains or website where Microsoft.com was mentioned following with the time and the location it was scanned.
Click on each link where Microsoft.com is mentioned to see how the domain was at the time it was scanned; this technic can also help you as analyst to find out how the domain looked in the past. Many phishing websites changed the website interface after abusing many people over the internet so this technic can reveal such activity.
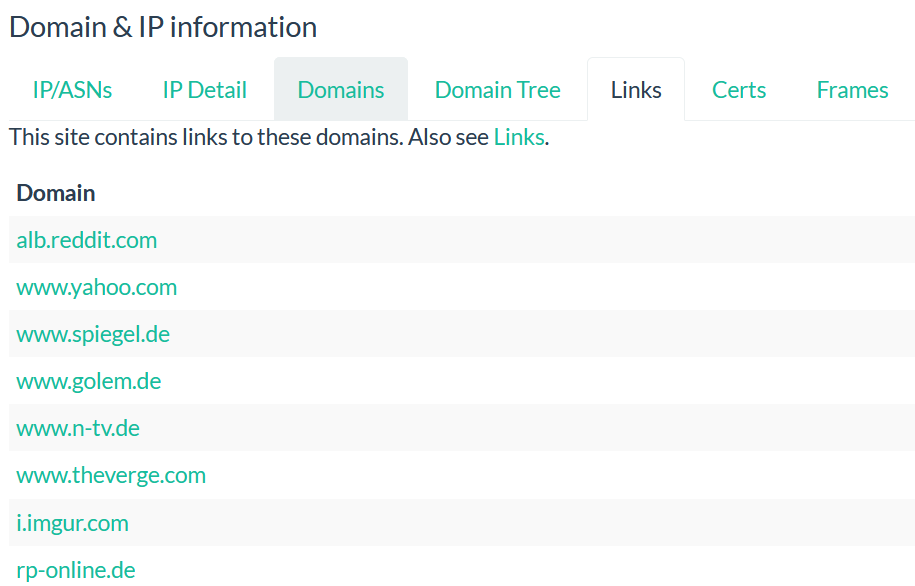
As you see, they are some domains or subdomains where Microsoft.com is not mentioned, we need to find out the relation between Microsoft.com and the domain.
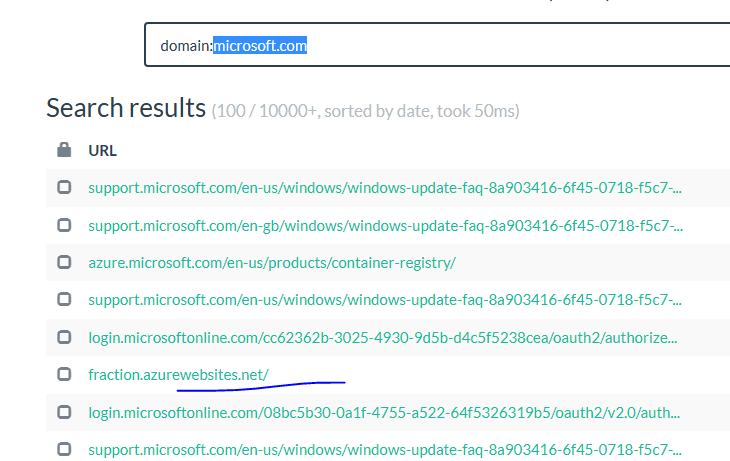
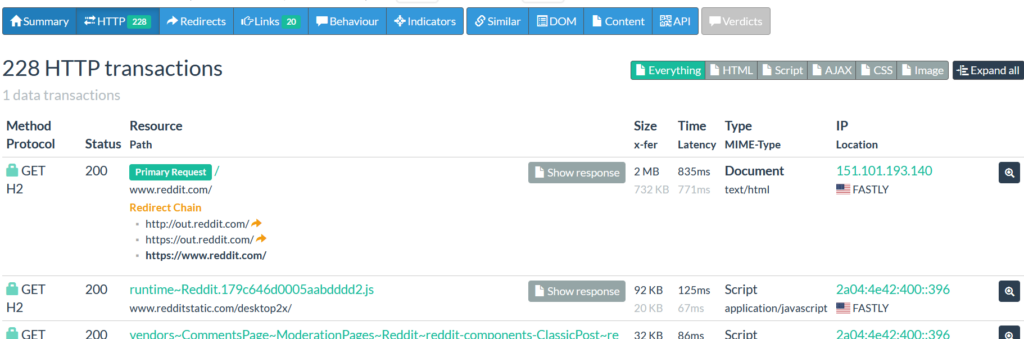
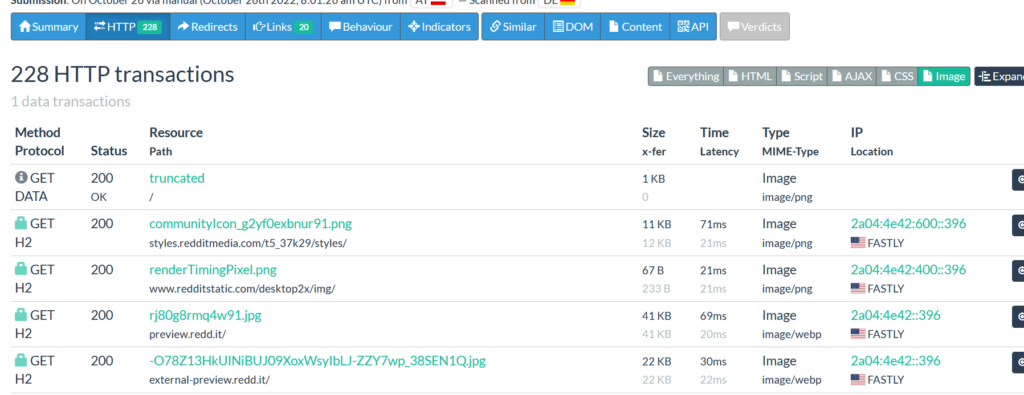
Click on fraction.azurewebsites.net, go to HTTP transaction, search for Microsoft.com
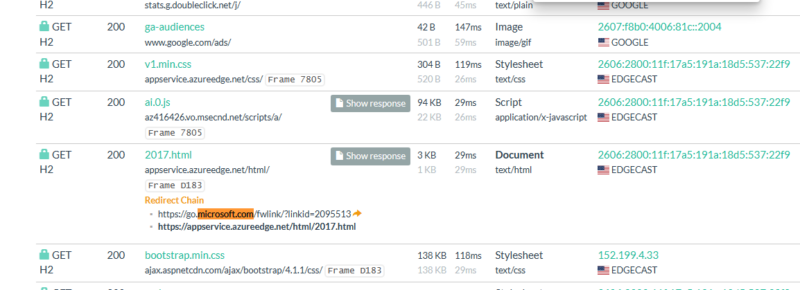
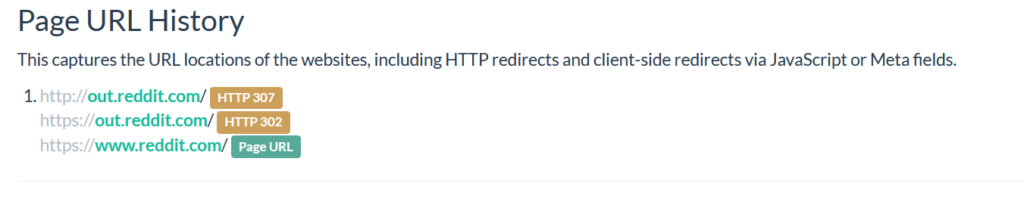
AS you can see, Microsoft.com is used as redirect chain. This technic is often used by the threat actor to hide their activities and it can be also used to find the correlation between the domains.
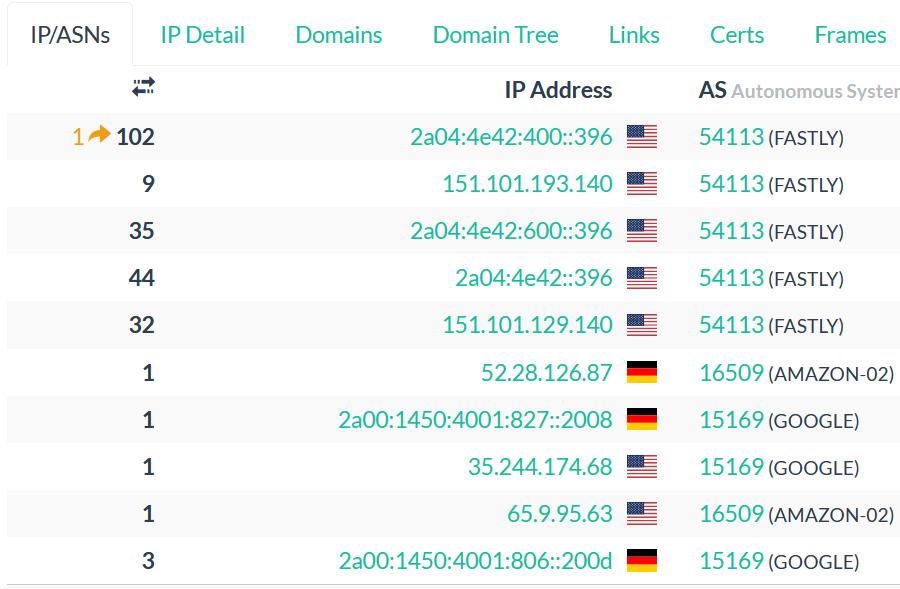
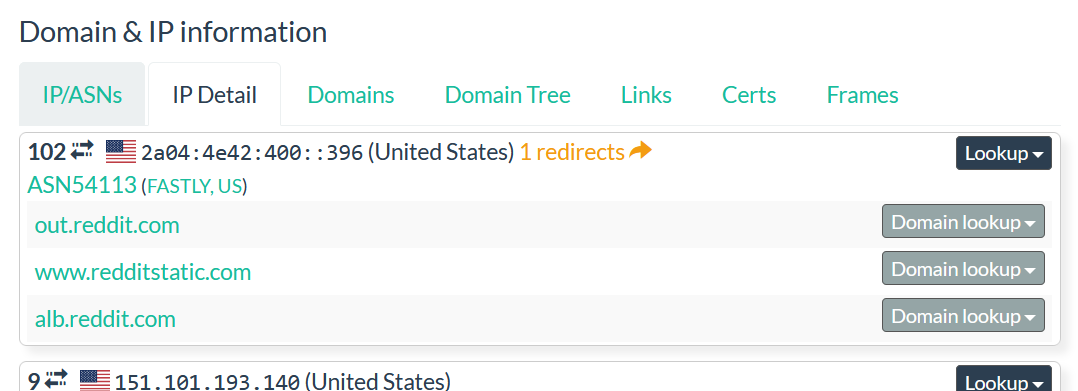
- Search for IPs
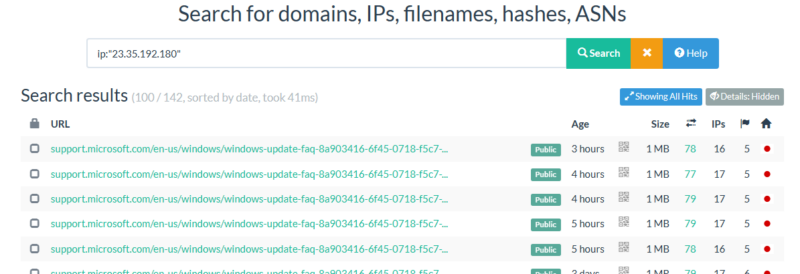
As you see in the image above, we entered the IP address 23.35.192.180 and we got the domains and subdomains behind the IP address. This technic can be used to find phishing related domain behind an IP address.
- Search for Hashes
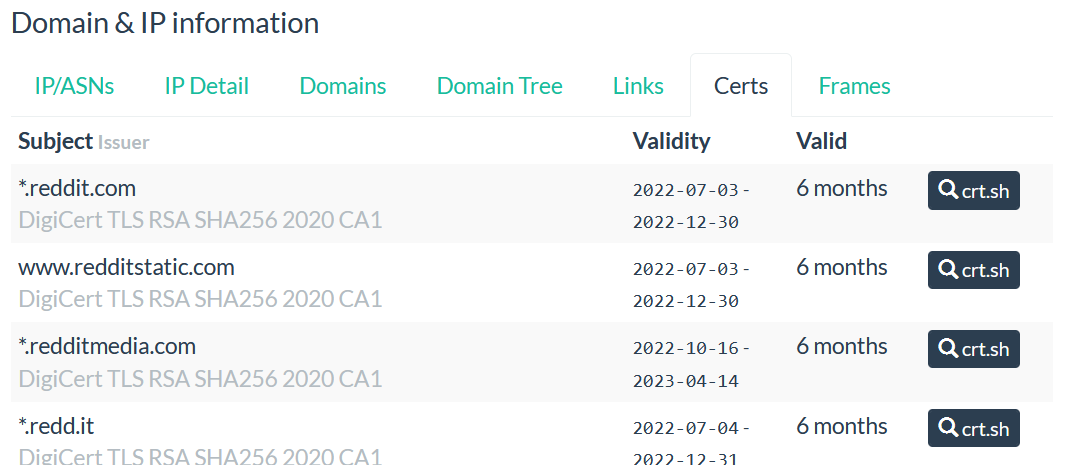
The hash can help you to make a correlation between the domains. Usually, the threats actor can use the same file but changed the domain, so this technic is good one to find such activity.
Example:
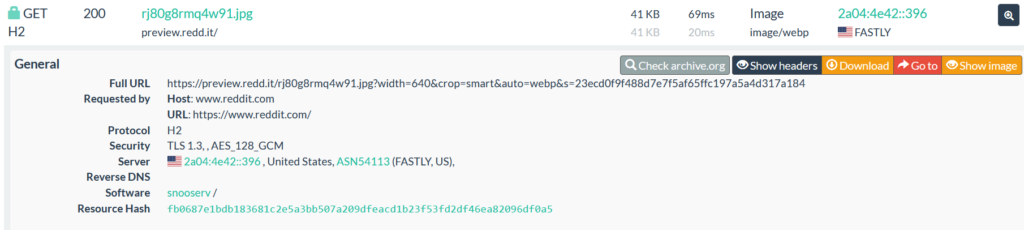
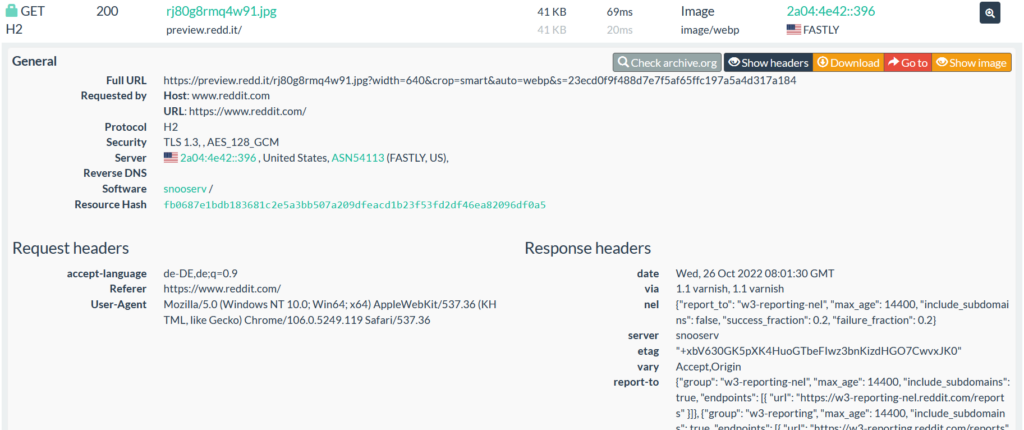
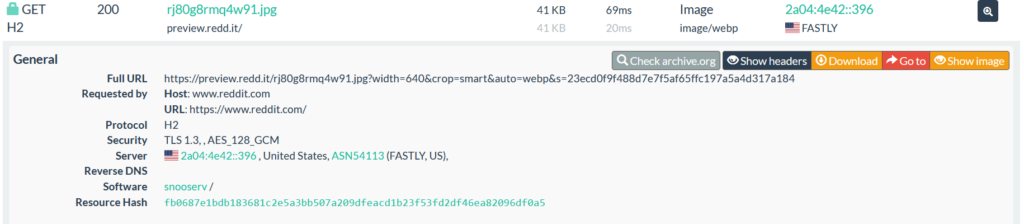
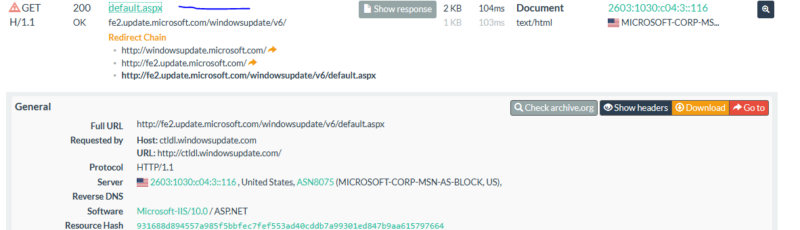
Click Microsoft.com, go to HTTP transaction, expand one http transaction request where the hash is available.
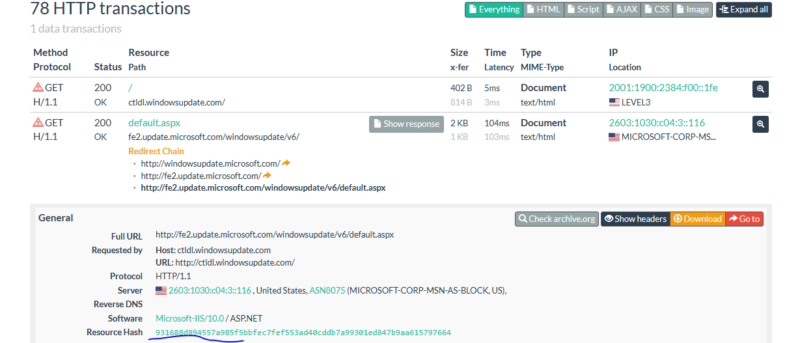
Hover the mouse on the hash and copy the hash, click on the Search menu and enter the query like you see in the picture below.
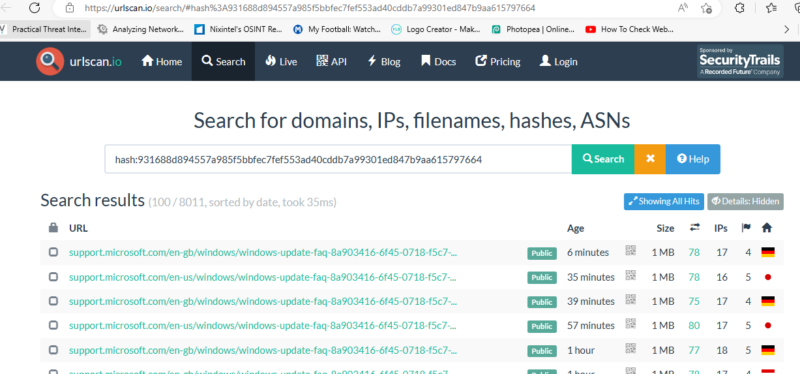
Now, we can see others websites that’s used the same hash.
- Search for Filenames
The same thing as we described in the previous section, the same filename can be used by the threat actor but with different domains name, we can use the same technic like we did to find the domain or website that used the filename. Be aware that the same file name does not mean that the file if the same, you need to compare the hash and also the file content to ensure that the files are the same.
Example:
From HTTP transaction, copy the file you wish to check
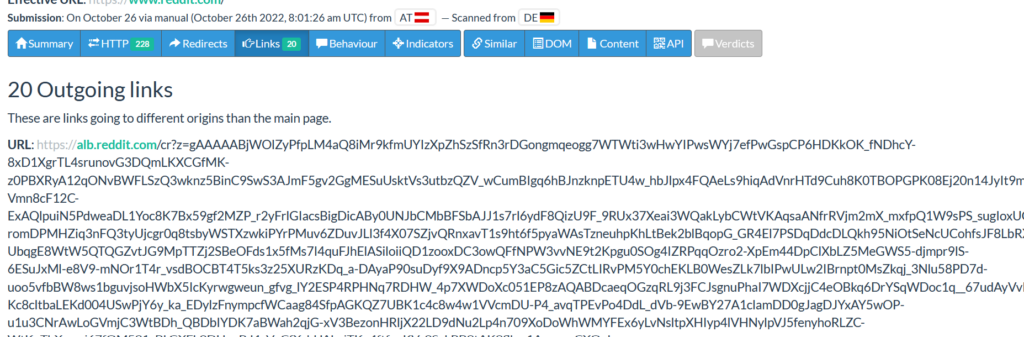
Go to search, enter the query like you see in the picture below, all the result from the search will appear.
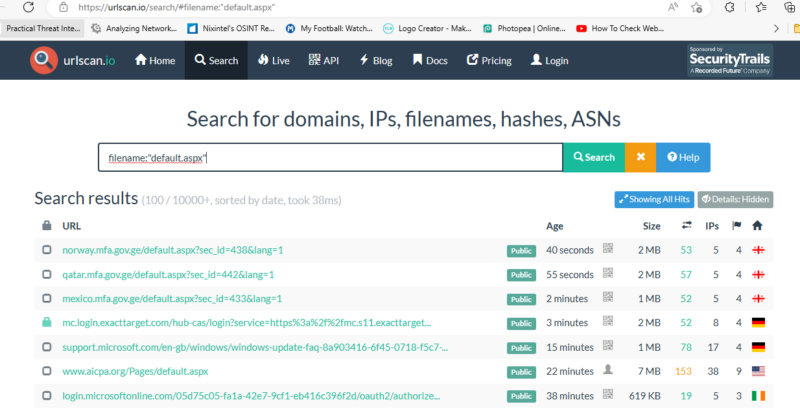
In order to verify if the file is unique, click on the URL, go to HTTP transaction compare the hash and the file content.
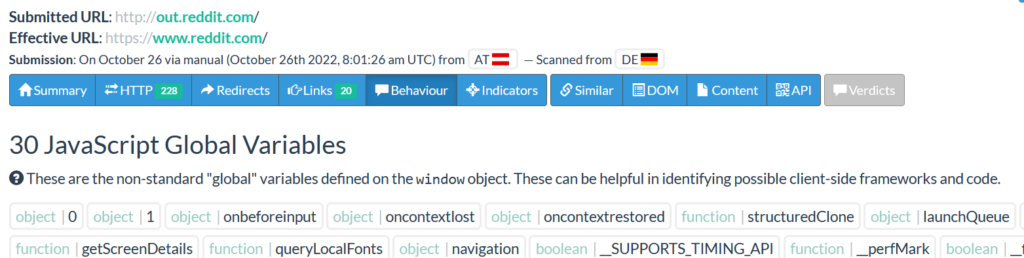
Like I said before, you can perform many types of searches using the search field. As a security guy you should know what you are looking for before making the search. The best way to learn is by practicing on the daily basis.
To conclude what we have explained, URLSCAN is very amazing tool that all security guys should use to make easier their job while analyzing different information like we showed in our examples.
The tool can help you save many times as it contains many types of queries that will help you to find more information during your analysis.
If you never used it, it is the time for you to start using and if you did not know the features we explained, then we suppose that you already know so enjoy.